The most recent articles
Find below the most recent articles sorted by date, to see the full archive please click here.

Could Open-Source AI Be the Ultimate Defense Against Digital Surveillance?
In an age where every click, search, and conversation potentially feeds into corporate data repositories, a quiet revolution is emerging from an unexpected corner: open-source

The State of Self-Driving Technology by 2030
By 2030, self-driving technology will be commercially viable in specific, constrained use cases—but far from the fully autonomous, ubiquitous reality once promised. This post explores

I Let an AI Take Care of My Plants – Here’s What Using PlantFocus Is Really Like
I’ve always liked the idea of having plants around me. The reality, though, is that my relationship with them has been… inconsistent. Some

Hidden Linux Performance Hack: RAM-Based Caching via /dev/shm
On most modern servers, RAM is abundant but underused. While CPUs and disks get all the optimization attention, RAM often sits idle, especially in web

Effectively Recover Data from Deleted Partition: RecoveryFox AI
Imagine your hard drive as a bookcase—neatly organized into sections (partitions) for easy management, privacy, and performance. But just as a shelf can collapse, partitions

SmartRingX Review: The Compact Health & Fitness Tracker You’ll Actually Wear
Why SmartRingX Is Redefining Wearable Health Tech Most health trackers force you to choose between functionality and aesthetics. SmartRingX eliminates that compromise. With a stainless

10 Gbit/s Uplink Intel Xeon Gold 5412U Dedicated Server: High-Performance Hosting
If you’re serious about high-performance hosting, it’s time to move beyond the standard 1 Gbit/s uplink. The new 10 Gbit/s uplink dedicated server featuring the

How to Fix FileZilla File Type Association Issue with Notepad.exe
You’re not alone if you’re using FileZilla and encountering an issue where Notepad.exe cannot be found due to a path problem. This common issue arises
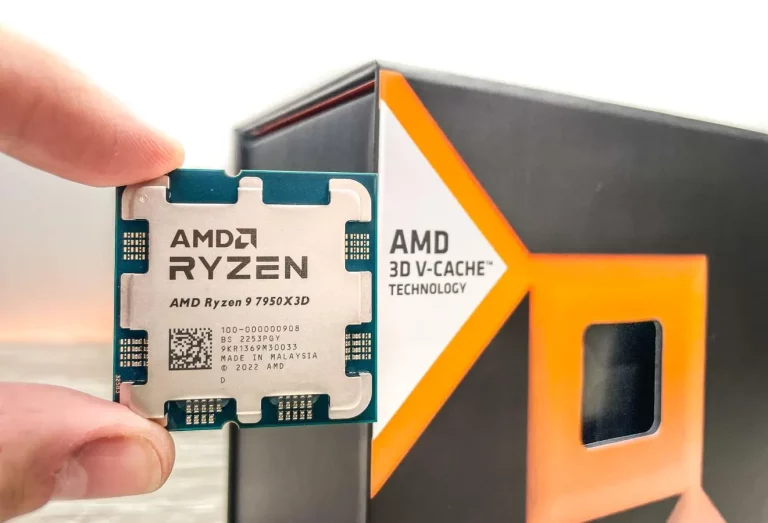
AMD Ryzen 9 7950X3D DDoS Protected Dedicated Server
The AMD Ryzen 9 7950X3D processor is a standout choice for handling heavy workloads. Offered by Dedicated EE, this dedicated server combines powerful hardware with practical

WonderFox HD Video Converter Factory Pro: A Comprehensive Review
In today’s digital age, multimedia software has become an essential tool for anyone who works with videos, whether it’s for personal use or professional projects.

Unveiling Qwen AI: A Comprehensive Look at Its Capabilities
Large language models have become pivotal tools for businesses, developers, and individuals. Among these innovations stands Qwen, a cutting-edge AI developed by Alibaba Cloud.
How DeepSeek Achieved Cheaper AI Processing Than OpenAI
The race to dominate the AI industry isn’t just about building smarter models—it’s also about who can deliver powerful AI solutions at the lowest cost.

Introduction to Containers and Docker on Linux: Basics and Setup
If you’ve ever heard the terms “containers” or “Docker” and felt a little out of your depth, don’t worry—you’re not alone. Containers are transforming how

PostgreSQL vs. MySQL: Comparison for Linux System Administrators
Understanding the differences between PostgreSQL and MySQL is crucial for managing databases effectively. Both PostgreSQL and MySQL are popular open-source databases, but they each have
Configuring the Linux Kernel: Basics and Considerations
The Linux kernel is the heart of every Linux-based operating system. It bridges software with the system’s hardware. Whether you’re trying to squeeze the best

Backup and Recovery Strategies: A Practical Overview for Data Protection
One of your most critical responsibilities for Linux Admins is ensuring the availability and integrity of your organization’s data. It’s not a glamorous job, but

Quick Guide: How to Brute Force with Burp Suite
This tutorial walks you through a simple brute force attack using Burp Suite. It’s hands-on, and while concise, it covers the essentials. For the best
Networking Basics in Linux: Network Settings and Multiple IPs
Setting up multiple IP addresses on a single network interface, allowing for more flexible and efficient management of services and resources is a common task

Process Management: Monitoring and Controlling Processes in Linux
As a Linux System Administrator, process management is one of the most crucial skills to master. Efficiently monitoring and controlling processes ensures the system runs
Galera Cluster: A Practical Guide to Setup on Debian/Ubuntu, Example With Two Nodes
Galera Cluster is a high-availability solution for MySQL databases, offering synchronous replication across multiple database nodes. Designed for MySQL, MariaDB, and Percona XtraDB Cluster, Galera
A Comprehensive Guide to Using rsync on Debian
As a Linux system administrator, managing file transfers and backups is a crucial part of your daily routine. Two popular tools for these tasks are
Shell Scripting Basics: Automation To Streamline Linux Administration Tasks
Linux administration is tightly linked to efficiency and precision. One of the best ways to achieve this is through shell scripting. Whether you’re managing hundreds

Using AppArmor on Debian: Enhancing Security on Linux Systems
Securing your system is no longer optional—it’s essential. As a Linux System Administrator, you are tasked with ensuring the security and stability of your systems,

Exploring Wireshark: A Powerful Tool for Sniffing Unencrypted Traffic
With countless devices and users connected to networks at all times, ensuring that sensitive data remains secure is a top priority. Yet, despite advancements in
